Editor's note: We have eroticism and other literary conventions in chinese literature: intertextualitypublished an updated guide to the Dark Web here.
You may have heard about this mysterious place on the Internet called the 'Deep Web'. Interest in the deep web and dark web arose following a few high profile data leaks, a growing interest in online privacy, references in mainstream media, and the widely publicized FBI investigation into online marketplace Silk Road that exposed the extent of online drug trafficking.
But what is exactly the deep web? Well it's not actually a 'place' but rather anywhere other than the visible web that is crawled, indexed and accessed through links fetched by search engines like Google. The deep web is actually several times bigger than the indexed web, and it encompasses a lot more than the illegal or otherwise questionable activities that it is often associated with – though there's certainly a lot of that going on, too. Let's start by clearing up some of the confusion among the different terms that tend to be thrown around while discussing the Internet's underground.
In simple terms, the Surface Web is anything that a search engine can find by crawling links and identifying content online, while the Deep Web is anything that a search engine can't find. The Dark Web on the other hand merely represents a smaller portion of the deep web that has been intentionally hidden and is inaccessible through standard web browsers.
To exemplify this a bit further, the deep web can actually include things like academic databases, which can be accessed through a normal browser but are not accessible to search engines.
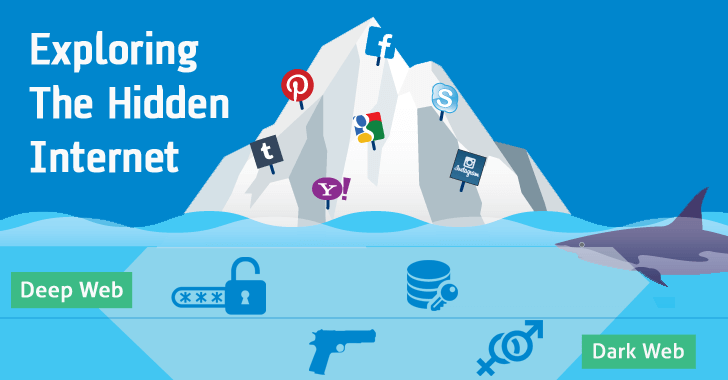
It also includes content within mainstream websites that is simply not set up to be accessed through a search engine. For example content posted on Facebook that is only available to the poster's friends, not the general public, or results for specific queries on a travel booking website – you simply can't get to the content by clicking through links like a search engine would.
The Tor network is the most commonly known place where dark web content resides. This anonymous network consists of thousands of servers located all over the world run by volunteers and online privacy advocates. Its name is an acronym for 'The Onion Router' in reference to its namesake routing technique, which creates a path through randomly assigned Tor servers, or nodes, before reaching whatever website you are visiting. During this process data packets are wrapped in successive layers of packets that get "peeled off" at each node until reaching the destination.
Here is a more technical explanation, but in concise terms, the result is that no one node knows the complete path between your computer and a website, only the last place the packet was, and the next place it will be. This makes it almost impossible for anyone to trace the traffic back to you.
While finding content on the dark web can take time and plenty of patience, technically, accessing the Tor network isn't that complicated at all. You simply need to download and install the Tor browser available for Windows, macOS, and Linux. It is no different from installing any other piece of software and it's very simple to use as it's just a modified version of Firefox.
If you're serious about the security of whatever it is you're doing on the dark web, it's worth running an entirely separate environment from your main computer and internet connection. Tails OS is a bootable operating system that's already preconfigured to maximize privacy and that you can run from a USB stick or a virtual machine. Tails has an installation wizard that guides you step-by-step through the process of setting up the software so that shouldn't pose much of a challenge either. Tails received a lot of press when it was disclosed that Edward Snowden was using it to avoid NSA snooping. Its sole purpose is preserving your privacy and anonymity online by relying on the Tor network and other tools to keep your activity secret.
Layering your location by starting at a random Wi-Fi hotspot and then connecting to a VPN before loading Tor will greatly increase your odds of anonymity.
We have written a more thorough, dedicated article to keeping yourself safe while surfing the seedy underbelly of the web. You can read that here.
 Trump tells '60 Minutes' that climate change will 'change back again'
Trump tells '60 Minutes' that climate change will 'change back again'
 India announces its largest solar rooftop tender
India announces its largest solar rooftop tender
 Michael Bublé's son goes home for the holidays between cancer treatments
Michael Bublé's son goes home for the holidays between cancer treatments
 India announces its largest solar rooftop tender
India announces its largest solar rooftop tender
 There's no evidence behind those 'Star Wars' boycott tweets
There's no evidence behind those 'Star Wars' boycott tweets
 Women are using this online map to report street harassment in their city
Women are using this online map to report street harassment in their city
 A couple's ruthless tipping policy is pissing off the internet
A couple's ruthless tipping policy is pissing off the internet
 Nintendo Switch 2 release date, price announced
Nintendo Switch 2 release date, price announced
 Watch Marines watching 'Gilmore Girls' and just try not to cry
Watch Marines watching 'Gilmore Girls' and just try not to cry
 Nintendo Switch 2 release date, price announced
Nintendo Switch 2 release date, price announced
 How you can help #Pizzagate victim Comet Ping Pong
How you can help #Pizzagate victim Comet Ping Pong
 Michael Bublé's son goes home for the holidays between cancer treatments
Michael Bublé's son goes home for the holidays between cancer treatments
 Inside the world's only 'flying eye hospital'
Inside the world's only 'flying eye hospital'
 Surprise! Taylor Swift and Zayn team up for '50 Shades Darker' soundtrack
Surprise! Taylor Swift and Zayn team up for '50 Shades Darker' soundtrack
 Inside the world's only 'flying eye hospital'
Inside the world's only 'flying eye hospital'
 A giant Jeremy Clarkson head keeps popping up to promote 'The Grand Tour'
A giant Jeremy Clarkson head keeps popping up to promote 'The Grand Tour'
 A closer look at 'The Dawning' holiday event in 'Destiny'
A closer look at 'The Dawning' holiday event in 'Destiny'
Nvidia outbids Microsoft, Intel to acquire chipmaker Mellanox for $6.9 billionYour social media photos could be training facial recognition AI without your consentAmazon to change vendor policy amid monopoly concerns, report saysHow to tell if your flight is on a Boeing 737 Max 8 before you book itNo one's more upset about the 'Walking Dead' premiere than this sobbing fanTesla hides hilarious secret message inside of Model Y invitationsU.S. women's soccer team sues for equal treatmentNew 'Destiny 2' catchTrump admin considers using social media to deny you benefitsTesla hides hilarious secret message inside of Model Y invitationsThe trailer for 'CRYPTO' just dropped, and cryptocurrency is good nowScooters took over SXSW and that's only the beginningNvidia outbids Microsoft, Intel to acquire chipmaker Mellanox for $6.9 billionPhiladelphia just banned cashless stores. Good.The trailer for 'CRYPTO' just dropped, and cryptocurrency is good now'Captain Marvel' star Brie Larson surprises cinema, serves up popcornTrump admin considers using social media to deny you benefitsToyota says selling fullComedy 'genius' and prolific 'web prankster' dies in tragic hit and runMichelle Obama and Hillary Clinton are finally rallying together A Sense of Agency: A Conversation with Lauren Oyler by Sheila Heti On Bei Dao’s Visual Art by Jeffrey Yang Cooking with Franz Kafka by Valerie Stivers Syllabus: Unexpected Dramaturgy by Lynn Nottage Caps for Sale by B.J. Novak On Peter Pan by Laurie Stone With Melville in Pittsfield by J. D. Daniels Prince and the Afterworld: Dorothea Lasky and Tony Tulathimutte Recommend by The Paris Review An Illegible Quartet and Choreographic Research by The Paris Review Madeleines by Laurie Stone Reading the Room: An Interview with Paul Yamazaki by Seminary Co Philistines by Nancy Lemann Citroën Cactus by Holly Connolly An Excerpt from our Art of Poetry Interview with Louise Glück by Henri Cole Child Reading by Timmy Straw A Pimp with a Heart of Gold by Liam Sherwin Inheritance by Hebe Uhart Lifesize Dioramas: At Carolee Schneemann's House by Hannah Gold The Locker Room: An Abercrombie Dispatch by Asha Schechter Happy Books by Sophie Haigney
1.2027s , 10192.578125 kb
Copyright © 2025 Powered by 【eroticism and other literary conventions in chinese literature: intertextuality】,Exquisite Information Network